🎯 Introduction: The Guardians of the Digital Ledger
In the traditional financial system, security is maintained by physical walls, armed guards, and fallible human laws. In the world of Bitcoin, security is maintained by Miners.
Miners are the specialized entities that provide the computational energy required to ensure the ledger is honest, the history is unchangeable, and the network is decentralized. In 2026, the “Hash Power” provided by miners has become a pillar of global economic stability—a massive, invisible energy shield protecting trillions in global wealth.
Section 1: Definition — The Network’s Immune System
Mining is not merely about “creating new coins”; it is the fundamental immune system of the Bitcoin protocol.
Definition
Miners' Role
The Role of Miners is to provide computational work (Hash Rate) that anchors the digital blockchain in physical reality. By expending real-world electricity to solve SHA-256 puzzles, miners make the cost of rewriting the history of the ledger significantly higher than any potential gain from cheating. This is known as Proof-of-Work (PoW).
Miners take the chaos of unconfirmed transactions and turn them into a “One-Way Street” of time and truth. Once a miner includes your transaction in a block, it is protected by the combined energy of every subsequent block.
Section 2: The Core Concept — The Separation of Powers
A common misconception is that miners “control” Bitcoin. In reality, the architecture is a brilliant system of checks and balances.
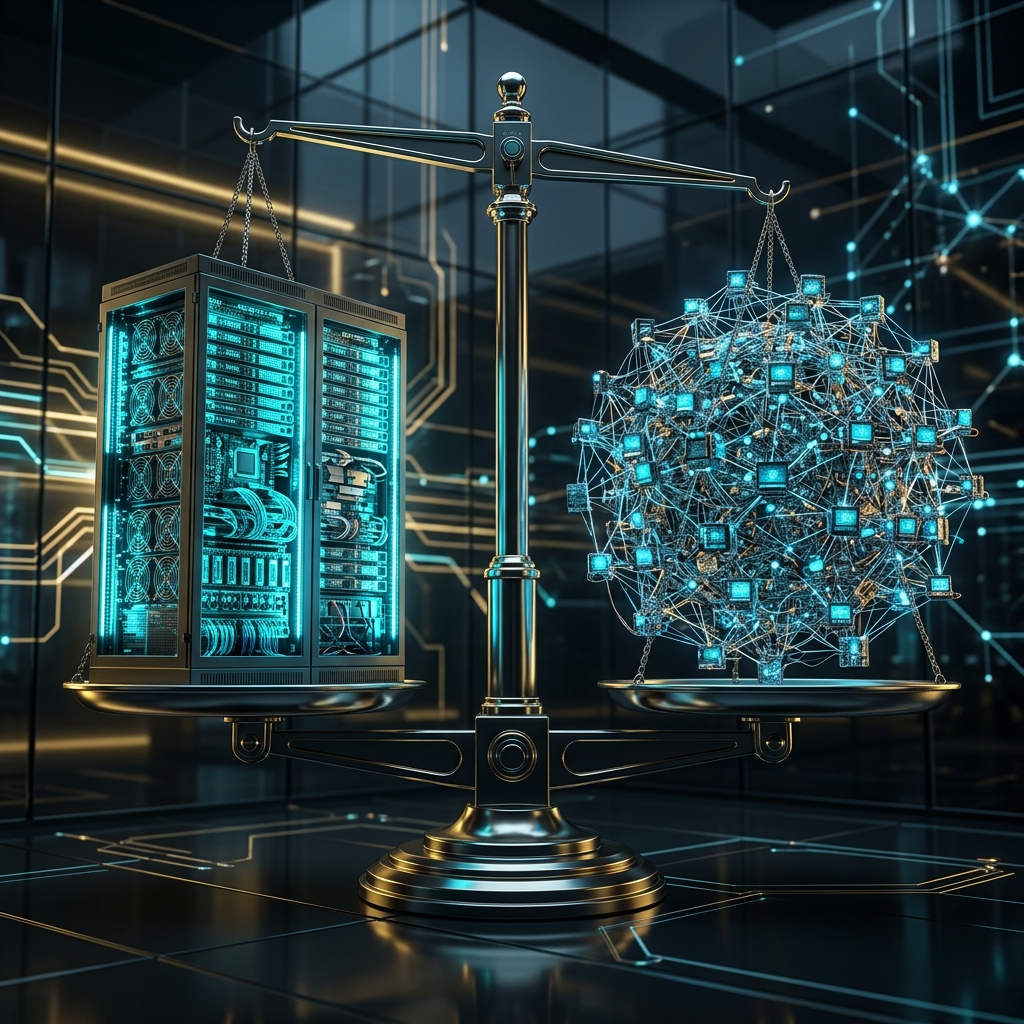
Think of miners as a construction crew building a skyscraper. They do the heavy lifting, but the Nodes are the building inspectors with the blueprints. If the crew forgets a support beam (breaks a rule), the inspectors condemn the building, and the crew goes unpaid.
Section 3: How It Works — The Energy Shield
The strength of Bitcoin’s defense is calculated by its Hashrate. This is the total number of cryptographic guesses being made every second by all miners globally.
Thermodynamic Verification
Miners convert physical energy into 'Proof'. This proof is physically impossible to fake; you either spent the electricity or you didn't.
Computational Interdependency
Each new block 'links' to all previous blocks. To change a transaction from 2015, an attacker must out-compute every miner that has worked since then.
Game Theory Equilibrium
The protocol pays miners in BTC. If a miner attacks the network, they crash the value of the very asset they are earning, making the attack financially suicidal.
Difficulty Calibration
If more miners join the 'Police Force', the network automatically makes the puzzle harder to maintain the 10-minute heartbeat of security.
Section 4: 2026 Threat Analysis (Nation-State Level)
Is it possible for a government to take over the network? In 2026, the numbers move this into the territory of the impossible.
In 2026, a government-level attack on the network has moved into the realm of the physically and economically impossible. Executing a 51% attack would require a capital expenditure of over $40 billion just for the specialized ASIC hardware, coupled with a lead time of several years to acquire and deploy millions of units. Even with the hardware secured, the energy requirement would exceed 200 Terawatt-hours—equivalent to the entire power grid of a G7 nation. This massive barrier ensures that Bitcoin remains protected by the thermodynamic laws of the physical world, making any attempt at a nation-state takeover a self-defeating financial catastrophe.
Section 5: Stratum V2 — Decentralizing Control
In the early days, “Mining Pools” took away some of the miners’ individual power. In 2026, the widespread adoption of Stratum V2 has returned that power to the individuals.
- Old System: The pool owner chose which transactions to include.
- Stratum V2: Each individual miner with a single rig chooses their own transactions. This makes the “Miner Shield” even more resistant to centralized censorship and government interference.
Section 6: Related Concepts — The Security Ecosystem
The role of miners is the foundation, but it interacts with every other layer:
- Bitcoin Mining Basics → The machines behind the shield.
- What is a Bitcoin Node? → Why you should run your own “Judge.”
- How Secure is Bitcoin? → The total cryptographic audit.
- Understanding the Halving → How the “Security Budget” changes over time.
- History of the Blocksize War → The moment nodes proved their dominance over miners.
Section 7: FAQ — Professional Security Insights
1. What happens if 51% of miners use a ‘Banned’ list?
Transactions might take longer to confirm, but because it is a global market, “Honest” miners in other jurisdictions will eventually pick up the transaction and include it in a block for the fee reward. Bitcoin was designed to route around censorship.
2. Is high energy consumption a ‘bug’ in the system?
No, it is a Feature. The energy usage is the “Cost of Security.” By making the network expensive to run, it makes it even more expensive to attack. This is what gives Bitcoin its property of “Digital Settlement Finality.”
3. Will miners stop securing the network after 2140?
No. By the year 2140, newly minted rewards will stop, but the network will be fueled entirely by Transaction Fees. As the global reserve asset, the competition for block space will provide more than enough incentive for miners to maintain the shield.
Section 8: Summary — The Unbreakable Wall
Miners are the high-performance engines of the decentralized world. By turning raw electricity into mathematical truth, they have created the first asset in history that cannot be seized, censored, or forged. In 2026, the security provided by the global mining fleet is the foundation of a Sovereign Future.
The ledger is protected. The math is absolute.
